|
|
||
|---|---|---|
| .github | ||
| .travis | ||
| acme | ||
| autogen | ||
| contrib/systemd | ||
| docs | ||
| examples | ||
| integration | ||
| middlewares | ||
| mocks | ||
| provider | ||
| safe | ||
| script | ||
| templates | ||
| types | ||
| version | ||
| webui | ||
| .dockerignore | ||
| .gitignore | ||
| .pre-commit-config.yaml | ||
| .travis.yml | ||
| adapters.go | ||
| build.Dockerfile | ||
| CHANGELOG.md | ||
| circle.yml | ||
| CODE_OF_CONDUCT.md | ||
| configuration.go | ||
| Dockerfile | ||
| generate.go | ||
| glide.lock | ||
| glide.yaml | ||
| LICENSE.md | ||
| Makefile | ||
| mkdocs.yml | ||
| README.md | ||
| requirements.txt | ||
| rules.go | ||
| rules_test.go | ||
| server.go | ||
| traefik.go | ||
| traefik.sample.toml | ||
| web.go | ||

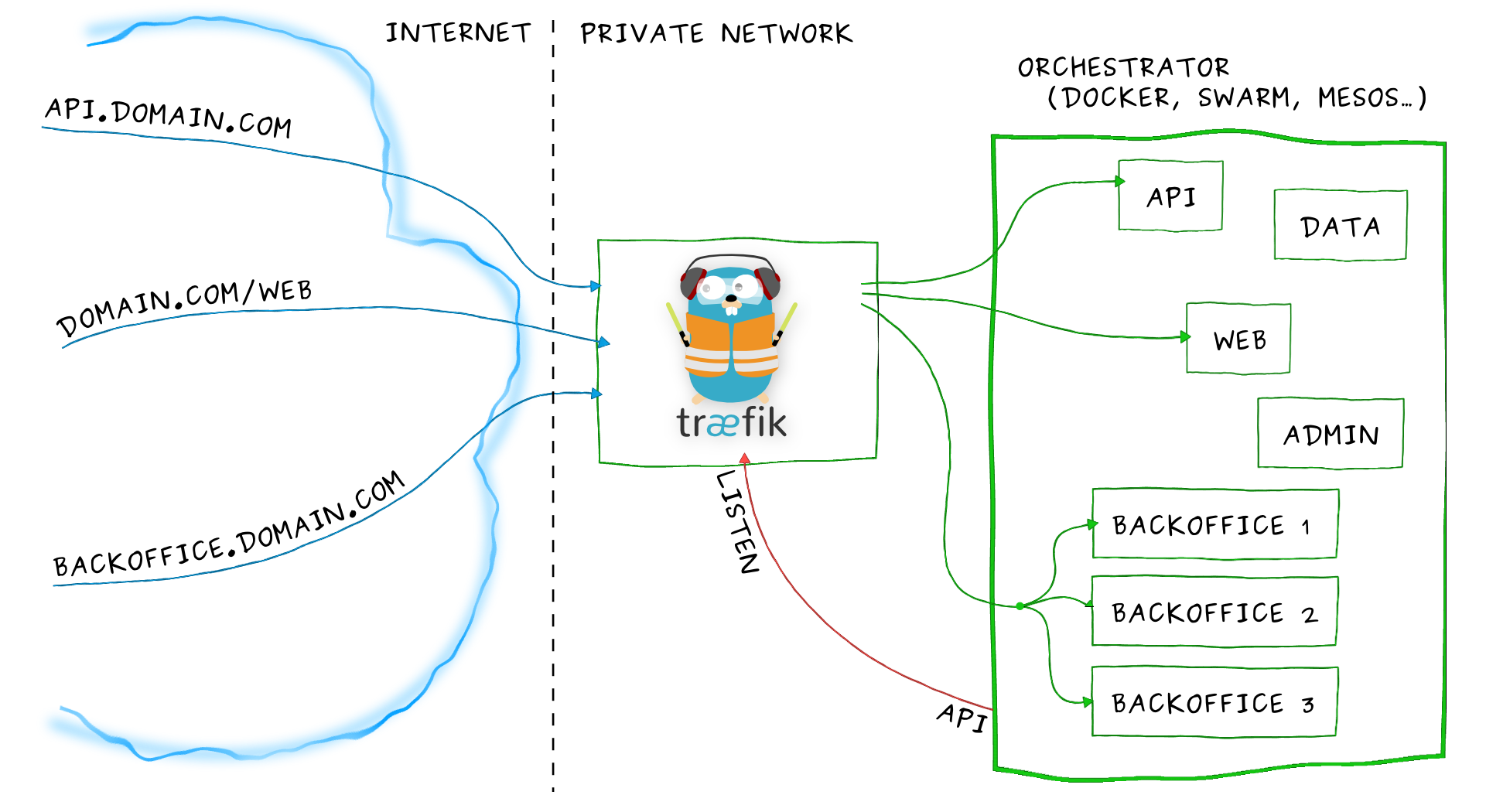
Træfɪk is a modern HTTP reverse proxy and load balancer made to deploy microservices with ease. It supports several backends (Docker, Swarm, Mesos/Marathon, Mesos, Kubernetes, Consul, Etcd, Zookeeper, BoltDB, Rest API, file...) to manage its configuration automatically and dynamically.
Overview
Imagine that you have deployed a bunch of microservices on your infrastructure. You probably used a service registry (like etcd or consul) and/or an orchestrator (swarm, Mesos/Marathon) to manage all these services. If you want your users to access some of your microservices from the Internet, you will have to use a reverse proxy and configure it using virtual hosts or prefix paths:
- domain
api.domain.comwill point the microserviceapiin your private network - path
domain.com/webwill point the microservicewebin your private network - domain
backoffice.domain.comwill point the microservicesbackofficein your private network, load-balancing between your multiple instances
But a microservices architecture is dynamic... Services are added, removed, killed or upgraded often, eventually several times a day.
Traditional reverse-proxies are not natively dynamic. You can't change their configuration and hot-reload easily.
Here enters Træfɪk.
Træfɪk can listen to your service registry/orchestrator API, and knows each time a microservice is added, removed, killed or upgraded, and can generate its configuration automatically. Routes to your services will be created instantly.
Run it and forget it!
Features
- It's fast
- No dependency hell, single binary made with go
- Rest API
- Multiple backends supported: Docker, Mesos/Marathon, Consul, Etcd, and more to come
- Watchers for backends, can listen for changes in backends to apply a new configuration automatically
- Hot-reloading of configuration. No need to restart the process
- Graceful shutdown http connections
- Circuit breakers on backends
- Round Robin, rebalancer load-balancers
- Rest Metrics
- Tiny official docker image included
- SSL backends support
- SSL frontend support (with SNI)
- Clean AngularJS Web UI
- Websocket support
- HTTP/2 support
- Retry request if network error
- Let's Encrypt support (Automatic HTTPS with renewal)
Demo
Here is a talk (in French) given by Emile Vauge at the Devoxx France 2016 conference. You will learn fundamental Træfɪk features and see some demos with Docker, Mesos/Marathon and Let's Encrypt.
Web UI
You can access to a simple HTML frontend of Træfik.
Plumbing
- Oxy: an awesome proxy library made by Mailgun guys
- Gorilla mux: famous request router
- Negroni: web middlewares made simple
- Manners: graceful shutdown of http.Handler servers
- Lego: the best Let's Encrypt library in go
Quick start
- The simple way: grab the latest binary from the releases page and just run it with the sample configuration file:
./traefik --configFile=traefik.toml
- Use the tiny Docker image:
docker run -d -p 8080:8080 -p 80:80 -v $PWD/traefik.toml:/etc/traefik/traefik.toml traefik
- From sources:
git clone https://github.com/containous/traefik
Documentation
You can find the complete documentation here.
Contributing
Please refer to this section.
Code Of Conduct
Please note that this project is released with a Contributor Code of Conduct. By participating in this project you agree to abide by its terms.
Support
You can join 
Træfɪk here and there
These projects use Træfɪk internally. If your company uses Træfɪk, we would be glad to get your feedback :) Contact us on
- Project Mantl from Cisco
Mantl is a modern platform for rapidly deploying globally distributed services. A container orchestrator, docker, a network stack, something to pool your logs, something to monitor health, a sprinkle of service discovery and some automation.
- Project Apollo from Cap Gemini
Apollo is an open source project to aid with building and deploying IAAS and PAAS services. It is particularly geared towards managing containerized applications across multiple hosts, and big data type workloads. Apollo leverages other open source components to provide basic mechanisms for deployment, maintenance, and scaling of infrastructure and applications.
Partners
Zenika is one of the leading providers of professional Open Source services and agile methodologies in Europe. We provide consulting, development, training and support for the world’s leading Open Source software products.
Founded in 2014, Asteris creates next-generation infrastructure software for the modern datacenter. Asteris writes software that makes it easy for companies to implement continuous delivery and realtime data pipelines. We support the HashiCorp stack, along with Kubernetes, Apache Mesos, Spark and Kafka. We're core committers on mantl.io, consul-cli and mesos-consul.
Maintainers
- Emile Vauge @emilevauge
- Vincent Demeester @vdemeester
- Samuel Berthe @samber
- Russell Clare @Russell-IO
- Ed Robinson @errm
Credits
Kudos to Peka for his awesome work on the logo ![]()